Open source WordPress powers more than 30% of the World Wide Web. Users publish over 41 million new posts on 15.5 billion pages for 409 million viewers every month.
This enormous surface area makes it a prime target for hackers. In 2018, 90% of all breached CMS sites came from WordPress according to a recent report by Sucuri.
[Source]
In this post, we break down five of the most common WordPress attacks — and offer solutions to mitigate risk.
1. WordPress Plugin Attacks
There are currently 54,666 WordPress plugins – a 22% jump from November 2018. Rapid growth has made this one of the most popular targets for cyber attacks. Here are two examples.
Cross-Site Scripting (XXS) Flaw
In March 2019, hackers targeted WordPress sites that use the Abandoned Cart Lite for WooCommerce plugin, which is installed on over 20,000 WordPress sites. After gaining access, they set up backdoors to take over vulnerable sites – starting by building a shopping cart and beginning the checkout process.
[Source]
After gaining access to the admin dashboard, they were able to view individual carts, customer data, and order totals.
Admins should make sure they’re using the latest, updated version of their plugins. In addition, they should review their database for potential script injections and delete any unauthorized admin accounts.
Remote File Upload Vulnerability in WordPress MailPoet Plugin
The WordPress MailPoet plugin is a newsletter editor that allows users to create newsletters, automated emails, post notifications, and autoresponders, among other features.
This plugin had a massive vulnerability that allowed attackers to inject myriad items onto the site. They could also use their access for malware injections, defacement, and/or spam.
Again, users updated their current plugin versions to secure their sites.
2. Hosting Vulnerabilities
In the summer of 2017, hackers took over newly created but not yet configured WordPress sites. They scanned for the following URL, which each new user receives: /wp-admin/setup-config.php.
Once hackers were in, they not only had access to the WordPress site but also the hosting account and all other sites on that hosting account.
To avoid this as a new WordPress user, you can safely install WordPress with a .htaccess file in the base of your web directory with a specific set of criteria. See here for full details.
3. Brute Force WordPress Attacks
Brute force attacks revolve around guesses. A hacker or a bot will guess as many password and username combinations as possible until they find success.
In December 2017, WordPress saw the largest brute force attack to date with 14 million attacks per hour. This was most likely due to a massive breach earlier that month where 1.4 billion clear text credentials emerged on the dark web.
[Source]
There are several ways to protect yourself from brute force attacks, including:
- Securing your website with regular security audits or a free tool like WPScan, which checks for vulnerabilities
- Using complex, hard-to-guess passwords
- Implementing multi-factor authentication (MFA)
See our prior blog post on preventing brute force attacks for more details.
4. Core and Theme Vulnerabilities
If users aren’t keeping sites up-to-date, they’re exposed to greater risks from outdated software. For example, in August 2018, a vulnerability emerged in tagDiv themes. Infections redirected page visitors to different sites and pushed them to verify and subscribe to different browser notifications.
A website firewall can help block the majority of new attacks on your themes, CMS, and plugins.
5. DDoS Attacks
A DDoS (or distributed denial of service) attack occurs when a high volume of traffic overwhelms a server and causes slow page load times and downtime. Even the most secure websites can experience DDoS attacks.
Volumetric attacks (most common), resource depletion attacks (that can slow a site indefinitely), and zero-day attacks (which target specific vulnerabilities) are three specific forms of DDoS attacks.
In 2018, Kinsta reported that it identified a 4650% spike in data transfer on a small WordPress site. The site usually generated 30-40 MB in bandwidth per day; however, out of nowhere, it jumped to 15-19 GB.
Kinsta checked the server logs. Entering several of the top IPs into Google search yielded proxy addresses – another red flag. To block the attack, Kinsta changed the site URL. From there, they recommended installing a firewall plugin like Wordfence or its own IP Deny tool. You can also take things a step further by migrating your site to either Cloudflare or Sucuri.
Many hosting sites automatically include a basic level of DDoS protection at no extra cost; however, you can also purchase additional coverage if you’re trying to protect a larger site.
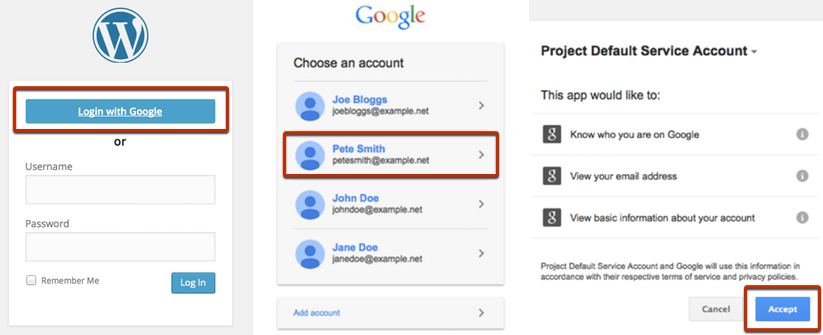
Use Google Apps Login for Extra Security on Your WordPress Site
You can also use Google Apps Login to add further protection to your WordPress site. Our tool helps ensure that only the right users authenticate onto your site – decreasing the risk that hackers will be able to enter and wreak havoc.